In today’s cyberthreat landscape, security must go beyond theory—it must be built, embedded, and sustained by design. That’s the promise of Microsoft’s Secure Future Initiative (SFI). Launched in November 2023, this multiyear security transformation marshaled the equivalent of 34,000 full-time engineers, representing Microsoft’s largest-ever cybersecurity effort.
1. Foundations Built on Three Core Principles
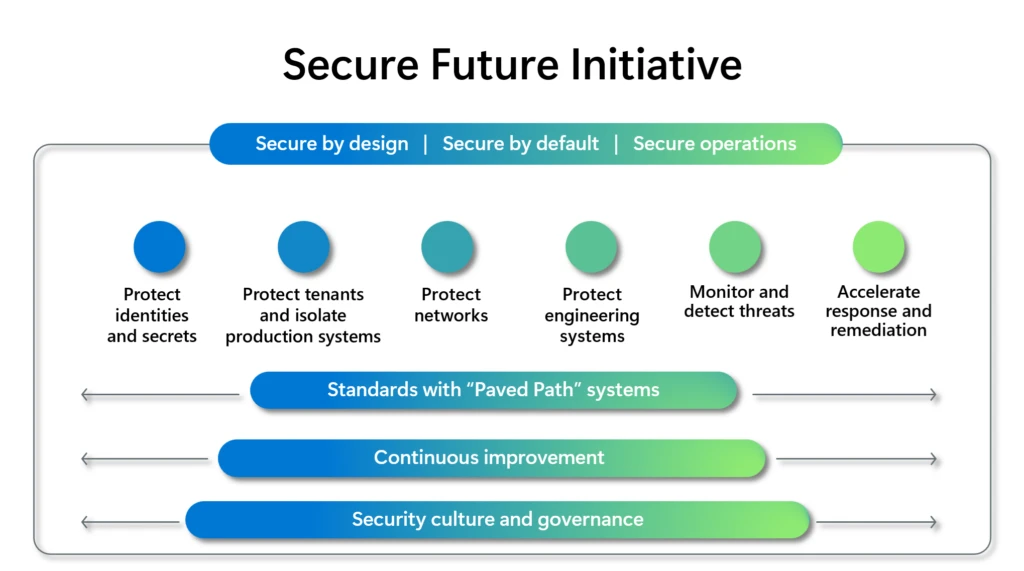
Microsoft anchored SFI around three guiding principles:
- Secure by Design: Security is prioritized from the outset of every service, system, and workflow.
- Secure by Default: Strong security configurations are enabled out-of-the-box—no optional toggles.
- Secure Operations: Continuous monitoring, adaptation, and refinement ensure resilience in the face of evolving threats
These are supported by a robust framework of security-first culture, governance, continuous improvement, and paved paths that elevate best practices to organizational standards.
2. The First Wave: Eight Pragmatic Patterns & Practices
Responding to repeated calls for practical guidance, Microsoft released the first wave of eight actionable patterns, each built around a clear structure: Name → Problem → Solution → Guidance:
- Phishing‑Resistant Multi-Factor Authentication (MFA)
Migrate from vulnerable MFA methods to stronger cryptographic approaches like FIDO2, passkeys, and certificate-based systems to minimize credential theft risks. - Eliminate Identity Lateral Movement
Architect access segmentation, enforce robust Conditional Access policies, and block risky guest sign-ins to prevent silent privilege escalation. - Remove Risky Legacy Systems
Decommission unmanaged tenants and outdated infrastructure—Microsoft eliminated over 5.75 million inactive tenants to reduce attack surface. - Standardize Secure Development Pipelines
Build security into CI/CD workflows using templates, Software Bill of Materials (SBOMs), and compliance “gates”. - Complete Production Inventory
Maintain a real-time catalog of assets, centralize telemetry, and retire unused systems to improve visibility and control. - Rapid Anomaly Detection & Response
Employ AI, user and entity behavior analytics (UEBA), and unified logging to detect threats quickly and automate response.
(The full set of eight extends beyond these, each addressing high-priority and complex security challenges directly encountered by practitioners today.)
3. Structuring for Reusability: The Patterns & Practices Taxonomy
Each article in the SFI patterns library follows a consistent taxonomy similar to design patterns in software—structured for clarity, adoption, and repetition:
- Pattern Name: A snappy label that captures the security challenge.
- Problem: Defines the threat or vulnerability in context.
- Solution: Shows how Microsoft addressed the issue.
- Guidance: Offers models, best practices, and implementation advice.
This consistency helps teams understand not just what to do, but why it matters and how to do it—making architectural concepts practical.
4. Why This Matters—for You and Your Team
The SFI patterns library is more than documentation—it’s an executable playbook that turns high-level policy into deployable engineering practices. What you gain:
- Accelerated security maturity
- Reduced friction in implementation
- Systems built to be secure from the start, secure by default, and secure over time
At Microsoft, this approach has already fueled measurable results: infrastructure hardened, identity risks reduced, legacy systems retired, and detection and response capabilities strengthened.



